People all over the world are using Xojo
to create powerful applications.
From citizen developers who learn to create apps to make their lives easier to full-time software developers, people are doing extraordinary things with Xojo.
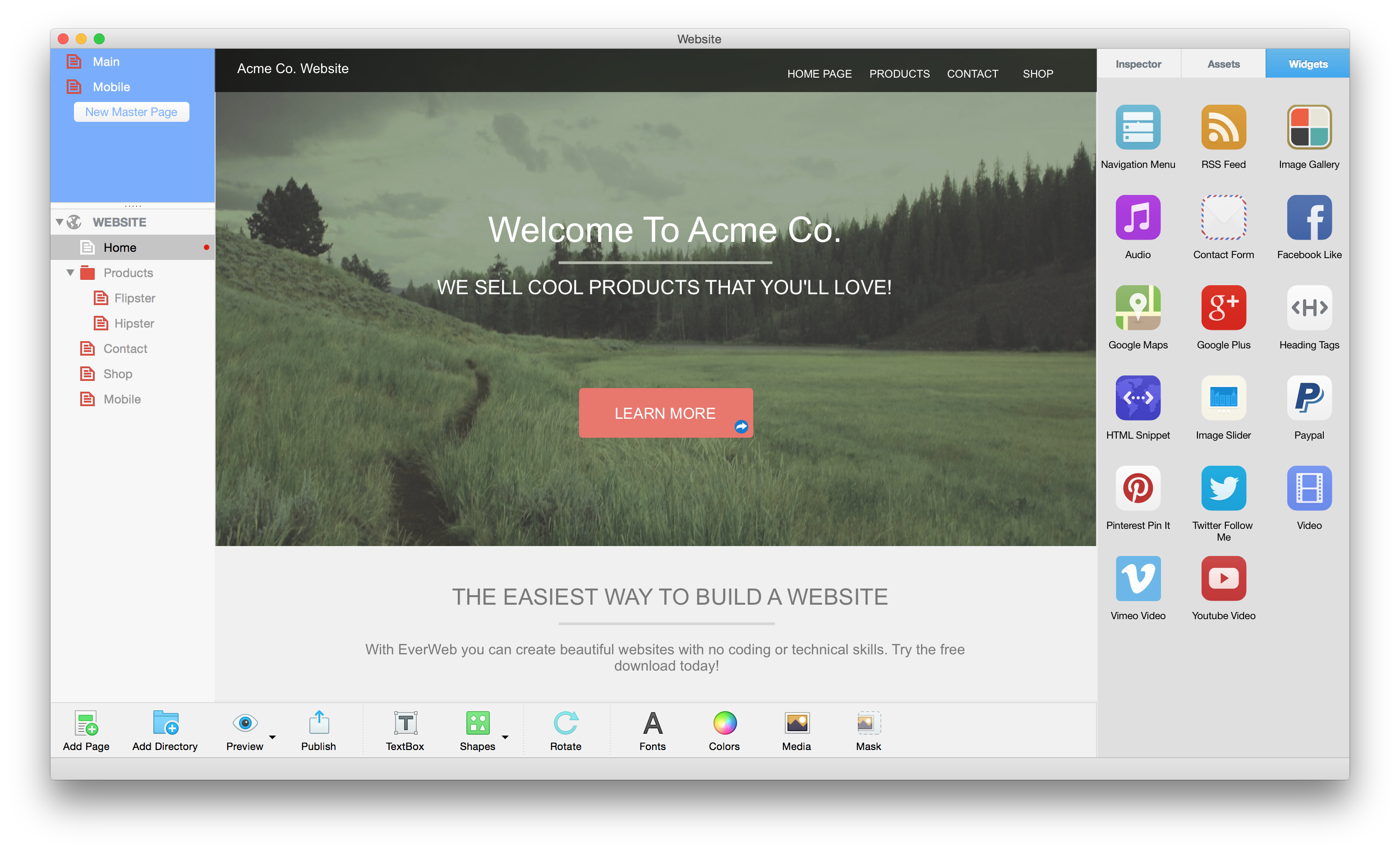
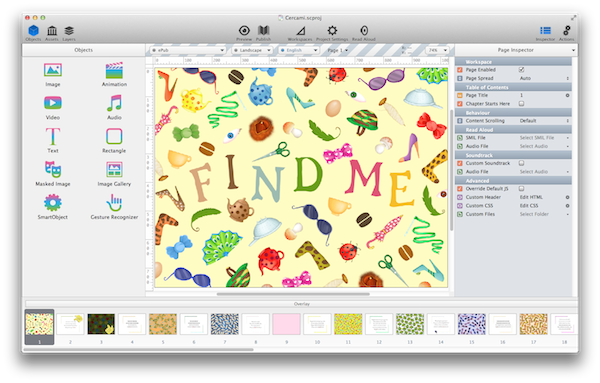
Everweb from Rage Software
Everweb is a drag and drop visual website builder that lets anyone create websites with no coding or design experience. EverWeb attracts users who want to create a website without relying on anyone else, but have no idea how to get started. EverWeb makes it super easy to start either from a template or from a blank canvas and design your website exactly how you want it without any technical skills.
EverWeb is the only website builder that integrates a native, downloadable application with a one click web publishing solution. No configuration is necessary to get your website online. It offers 100% freedom in design while producing super fast HTML5 and CSS3 websites.
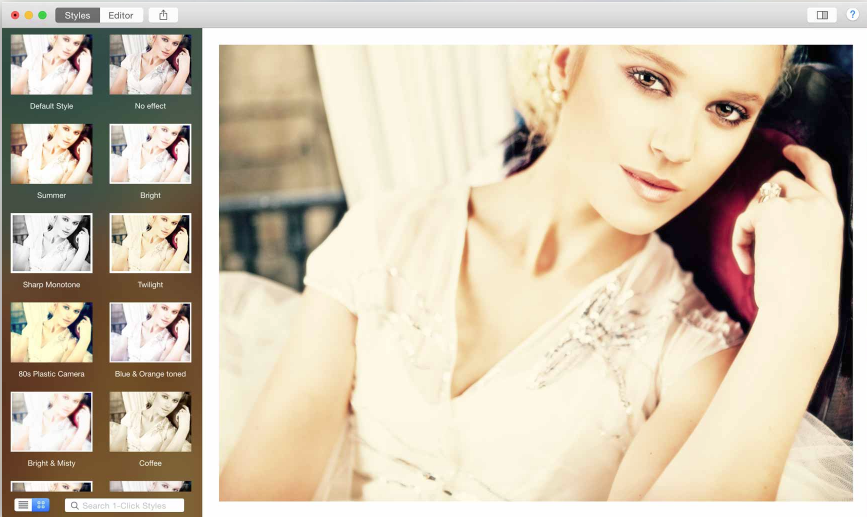
Shine from Ohanaware
Shine, which was designed to allow users to quickly and easily enhance digital photos by adding light rays, lens flares, tinting and other effects. For example, one morning the developer, Sam, took a photo of a sunflower with the sun behind him. He then used Shine to add a light source, light rays, a lens flare and tint the photo. The result was a photo that looked like it was taken as the sun was setting from a direction the sun would never set!
Using Xojo, Ohanaware has made a name for themselves in the Mac community as the developers of polished and professional photo editing software.
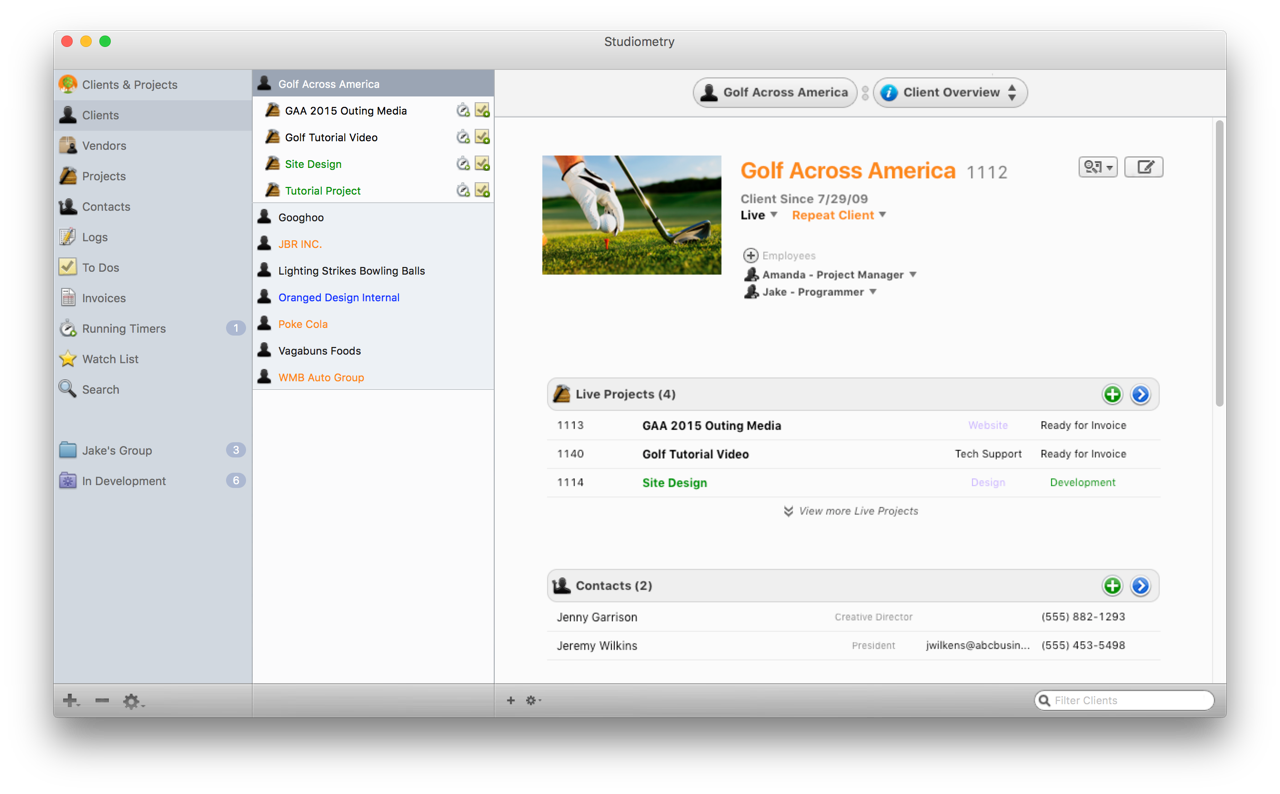
Studiometry from Oranged Software
Studiometry is a business management tool that tracks clients and projects from start to finish. It helps track everything from potential clients, estimates, meetings and tasks, work, invoices, payments, and summaries. Thanks to its flexibility and helpful industry templates, it can be used effectively in almost any industry. Studiometry is a one stop shop for managing any business that has clients or projects. Studiometry is tailored for businesses with 1-50 users and has approximately 10,000 users.
Previously written in Objective-C, the developer ran into several issues, forcing them to maintain two separate code bases. Any update to a class in Studiometry on the desktop would require a separate update to the Objective-C source code. Xojo's iOS support completely removes the need and hassle of developing a separate code base in Objective-C or Swift.

Background Eraser from Worksdem Software
BackgroundEraser lets you easily remove the background from your images. BackgroundEraser has been a great success, in less than 5 months it has been purchased by more than 5,000 users.
Prior to finding Xojo, Worksdem used Visual Basic and C++, but they really needed a cross-platform solution to deliver the kinds of projects they were being asked for. Xojo halved their development time and they were able to satisfy every customer request for a macOS and Windows version of their app.
Worksdem's applications are in use by 60,000 people and that number grows daily.
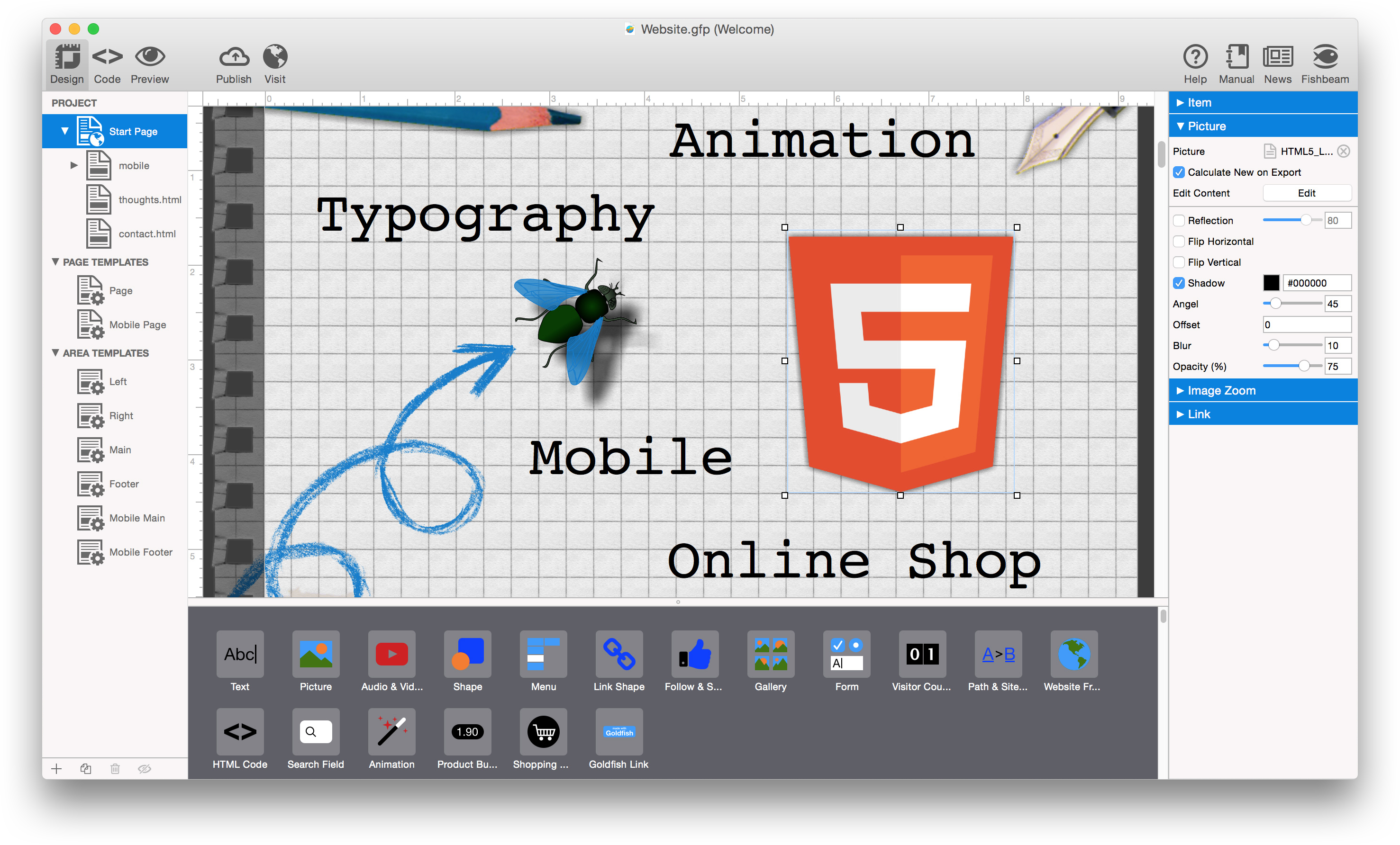
Goldfish from Fishbeam Software
Goldfish is a drag and drop website builder that features things like blogs, custom forms, online shops, search, animations, integration of Facebook, YouTube Twitter and more. It includes views for mobile devices and you can do all of this without coding. Once a website is finished, it can be uploaded with the integrated FTP publisher to any web server.
With over 15,000 customers, Goldfish already has everything integrated that you need for a website, like an online shop with PayPal checkout. By learning Xojo, Pellot was able to unify his interests - programming, publishing and graphic design, to build a successful business that continues to grow!
Pubcoder
PubCoder is a desktop app for creating highly interactive ebooks for any platform, in every language. With PubCoder every object on a page can respond to events like touch, pinch, swipe, device tilting or shake, and interact with other objects, moving, rotating or scaling them but also playing videos, sprite animations and sounds.
To use PubCoder you don’t need to write a single line of code. So everyone who wants to create and self-publish a book can do it with PubCoder: authors, illustrators, graphics, developers, but also parents who want to quickly create a story or a photo-album for their children.
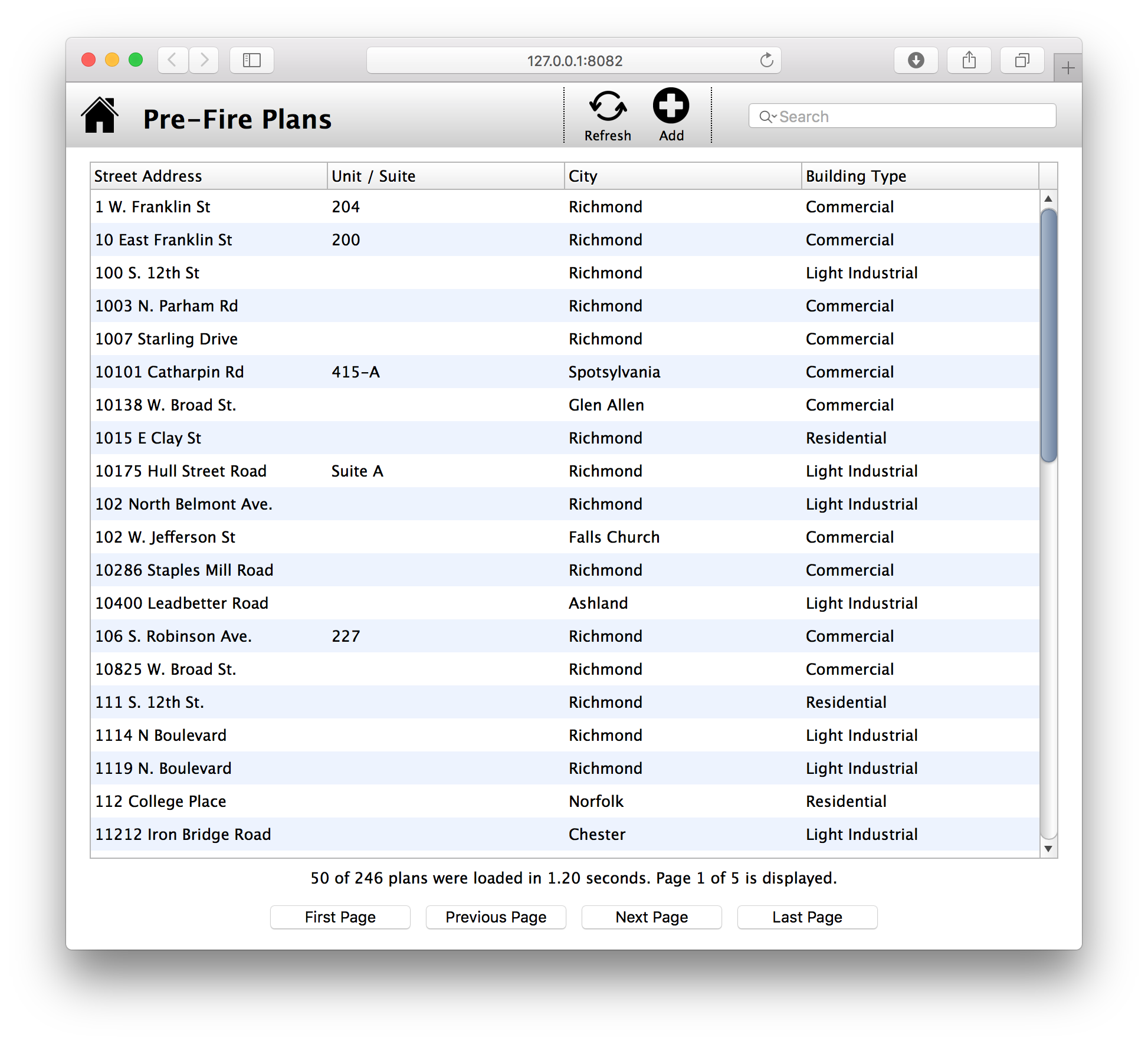
Tim Dietrich - Custom Software Developer
Tim Dietrich was feeling burned out and ready for a change of pace. He was hitting a wall with FileMaker plus he was growing interested in developing mobile apps. A fellow FileMaker developer had made the switch to Xojo and suggested Tim try it out. He instantly felt comfortable, Xojo was intuitive and it felt like he had been using it for years. He instantly thought the IDE and language were nice, and the overall process that you go through when developing Xojo-based solutions is logical and made a lot of sense.
Today, most of the work Tim does is with Xojo. While he originally started using it to develop iOS apps, he’s since used Xojo to develop web apps, APIs, console apps, Web bots - even content servers for Apple TV (tvOS) apps.
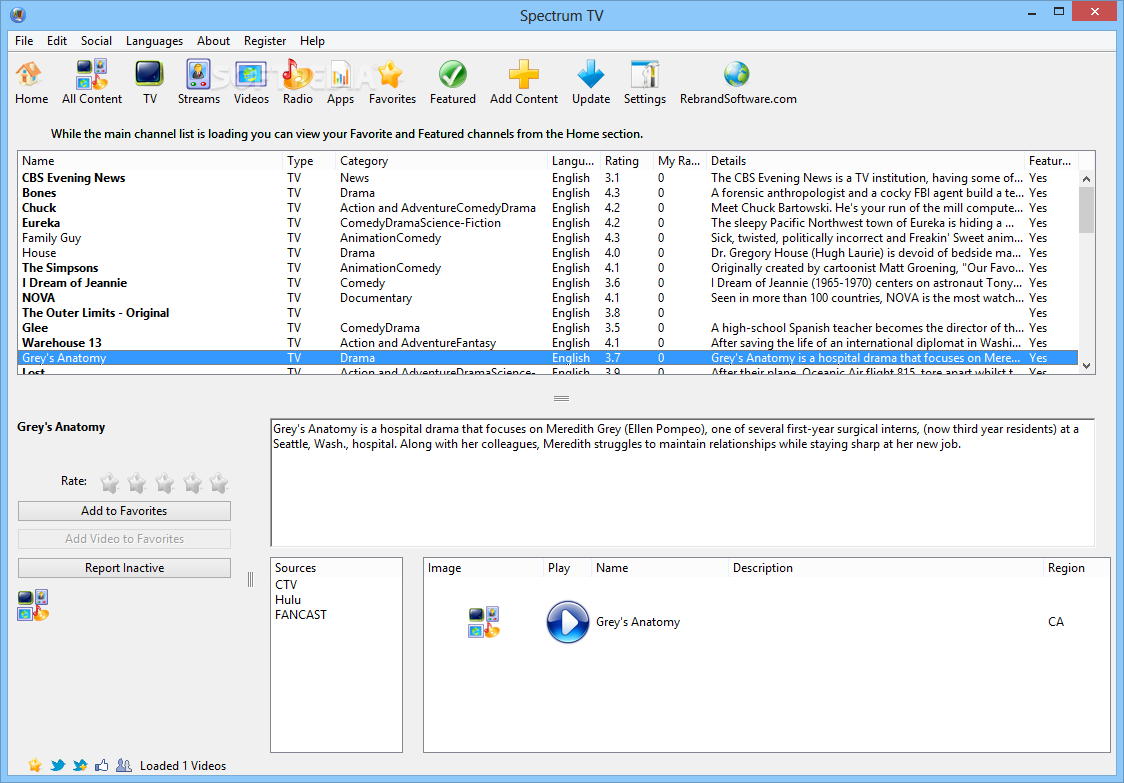
Spectrum TV from Rebrand Software
As more companies continue to expand their digital marketing programs to increase traffic with branded applications, Mike Gibson knew he needed to speed up his current processes. They were using Visual Basic, but VB required tedious re-writing of code to produce macOS and Linux versions of each app. Mike was looking for a tool that allowed his team to write code once and deploy it on Windows, macOS and Linux, along with an active coder community and more ease of coding.
Using Xojo, Rebrand Software has been able to quickly improve the quality of their apps across all platforms, while focusing more the creativity and uniqueness of their applications, resulting in 25% more revenue.

Burning Man Festival
Burning Man is an annual art festival that takes place in the desert with approximately 65,000 attendees. While heading to the Burning Man Festival, attendees will take a gravel road that ultimately opens up into 8 traffic lanes. These lanes, essentially a giant parking lot, go on for over 5 miles, with people waiting for processing to enter the event. Now imagine all of these people trying to leave. That process was taking 8 hours or more. One of the festival planners recognized they needed a communications system to help with traffic and emergencies, like Amber Alerts and other PSAs.
They decided they needed an app to automate a variety of messages that would be sent them via a radio station. The results of implementing the radio station are profound. Upon entry to Burning Man, the details transmitted on the radio station had each attendee totally prepared for processing at the gate, eliminated many of their questions, turned away the majority of the stowaways and ultimately cut entrance time from 7 hours to 2.5 hours. The exit process was seamless and manageable. They never had to pulse cars, never had a backup and never had more than a 2 hour gate time leaving the city.